What Is Log Management?
Log management is a critical function within IT and business operations that focuses on handling and making sense of the log data generated by computer systems, networks, and applications.
Every action in an IT environment, from user activity to system errors, generates logs through details. These detailed records capture what’s happening within your systems at any moment.
The log management process involves several key activities:
- Collecting the log data from various sources.
- Storing the log data efficiently.
- Organizing it for easy access.
- Analyzing the log details to gain meaningful insights.
All these activities are not just to keep records but to actively use the data to improve system performance, detect anomalies, and support decision-making.
Log Management Basics: What is a Log File?
A log file is a fundamental element in computing and IT. Simply put, it provides a record of events that occur within a technology system or network. Consider it a detailed diary that your computer systems keep to record every possible activity in a log file whenever something happens in the system. This can be user actions, an event of a program running, or even an error occurring.
Details stored in log files are essential for several reasons:
- They provide a chronological record of events, which can be incredibly helpful for understanding the system’s behavior. For instance, IT professionals can look back at the log files if something goes wrong to determine what happened and why.
- Log files provide the raw data collected, analyzed, and monitored to keep IT systems secure and functioning efficiently.
- Without these files, it would be like flying blind – there would be no way to know what’s happening in your systems or how to fix issues when they arise.
Log Management vs. Application Performance Management
When discussing managing IT systems, two key concepts often come up: Log Management and Application Performance Management (APM).
Both are equally important in an organization focusing on IT health and efficiency. Let’s break them down in a simple yet comprehensive way.
Log Management
We’ve already touched on log management: it’s all about handling the log files that systems generate. These logs record user activities, system errors, or security breaches and store them to analyze further.
Logs are rich repositories, chronicling security breaches, user activities, and system errors. Organizations can delve deep into various aspects of their IT operations by analyzing these logs.
While a security risk register is invaluable for identifying risks, particularly those uncovered through log analysis, log management’s utility is wide. It is like maintaining a comprehensive journal of your IT environment, offering insights into system performance, security, and troubleshooting.
This broader view enables organizations to pinpoint the root causes of a wide range of issues, not just those confined to security.
- It centralizes and indexes logs.
- It offers a unified view of data and notifications to help teams collaborate effectively.
- It helps businesses stay compliant with policies and industry regulations.
- It helps in monitoring anomalies or inactivity to gauge system health. It helps in detecting specific log events and patterns in log data.
Log management continually monitors and analyzes every facet of the IT environment, safeguarding against various risks and enhancing overall operational efficiency.
Ideally, you’d prioritize gaining insights into system performance security and troubleshooting issues. It’s like keeping a detailed journal of everything in your IT environment.
Application Performance Management (APM)
APM focuses more on specific applications’ performance and user experience. It’s about monitoring and managing software applications’ performance, availability, and user experience.
APM tools determine how fast an application runs, how effectively and whether any issues affect the user experience. It’s like having a constant health check on your applications to ensure they are performing at their best.
While both log management and APM deal with maintaining IT systems, they differ in some aspects as follows:
| Point of Difference | Log Management | APM |
| Focus | Recording and analyzing data on system events | Real-time monitoring and managing of application performance. |
| Purpose | Helps diagnose problems after they occur, understand system activity, and ensure security | Ensures that applications are running smoothly and efficiently, enhancing the user experience |
| Data Used | It relies on stored logs in a system and cloud. | Leverages performance metrics and user experience data, like load times. |
Why is a Log Management System Important?
A log management system can help enterprises manage vast amounts of data, turning a potential overload of information into actionable insights.
Also, in a time when data-driven decisions are key to success, a robust log management system is indispensable for any organization that aims to stay competitive and secure.
Improved Operations
Log management plays a pivotal role in enhancing the operational efficiency of IT systems. It is a powerful tool for IT professionals, allowing them to maintain high performance and reliability in their networks and systems.
Here’s how:
- Streamlined troubleshooting: Log files provide a chronological record of events, making tracing the root cause of issues easier. For example, if a server crashes, logs can help pinpoint whether it was due to a software error or a hardware failure.
- Automated alerts: Log management systems help set up to send alerts for unusual activities, enabling quicker response times. For instance, an alert can prompt immediate investigation if there’s a sudden spike in resource usage.
- Efficient problem-solving: With a comprehensive log management system, IT teams can quickly sift through vast amounts of data to find relevant information. This efficiency reduces downtime and ensures that problems are resolved quickly.
Better Resource Usage
Organizations thrive when they have effective IT management in place. Log management comes a long way to achieving this by providing insights into how their systems and applications consume resources like memory, processing power, and network bandwidth by analyzing log data.
- Optimized system performance: Log data helps fine-tune system resources for peak performance. For example, it identifies underused servers and helps allocate underutilized resources.
- Energy savings: Efficient resource usage translates to energy savings, particularly in large data centers, where overuse can lead to excessive energy consumption.
- Cost-effective operations: Organizations can reduce unnecessary expenditures on IT resources with careful monitoring and adjustment based on log data.
User Experience
Businesses can significantly enhance the user experience by leveraging log data and creating more efficient, user-friendly, and reliable applications. This boosts user satisfaction and contributes to long-term customer loyalty and business success.
Further, log management enhances user experience in the following manner.
- Error detection and resolution: IT teams can quickly identify and fix bugs that negatively affect user experience by analyzing error logs. This proactive approach minimizes downtime and user frustration.
- Customizing User Interactions: Analyzing user behavior through logs allows for a more tailored experience, adjusting layout and features to better align with user preferences and needs.
- Identifying Bottlenecks: Logs can highlight areas where users face delays or issues, allowing for targeted improvements. For instance, if log data shows that a specific feature causes an application to slow down, developers can work on optimizing that feature.
Understand Site Visitor Behavior
Understanding the behavior of visitors on your website or application is crucial for tailoring user experiences and improving engagement.
Log files can reveal a wealth of information about how users interact with your site, which pages they visit, and what actions they perform.
- Track user pathways: Logs can show a user’s journey through your site, highlighting popular paths and potential areas of confusion or abandonment. For example, it might need improvement if many users exit the site from a particular page.
- Optimize content strategy: Analyze the pages and features that users visit the most, which help align your content strategy to match user interests. For instance, if logs show high engagement with certain topics, you can focus more on similar content.
- Enhance marketing efforts: Understanding user behavior through log management helps create targeted marketing campaigns. If logs indicate that a specific demographic spends more time on certain sections, you can utilize various marketing channels and customize the marketing to match users’ preferences.
Added security
You cannot undermine the role of cybersecurity in a largely connected world. Therefore, if cybersecurity is your priority, then consider leveraging log management.
Ultimately, you’ll get to identify security incidents, and log management can help prevent them. They are the first line of defense in detecting unusual activities that could signify a security threat.
- Detect anomalies and threats: Log files can help identify patterns of suspicious behavior, such as repeated failed login attempts or unusual data access patterns, which could indicate a security breach.
- Facilitate incident response: In the event of a security incident, logs provide valuable information for understanding the scope and impact of the breach, aiding in a swift and effective response.
- Ensure regulatory compliance: Many industries have regulations that require certain logs to be kept for compliance purposes. For instance, logs can be critical in demonstrating compliance with data protection laws like GDPR or HIPAA.
The Log Management Process
The log management process is a systematic approach to handling the vast quantities of log data generated by computer systems and networks. It involves several key steps, each crucial in ensuring that log data is used effectively and efficiently.
Here’s an overview of the process and its steps.
1. Log Data Collection
This initial step involves collecting log data from every corner of your IT environment. This includes servers, applications, network devices, and other technology that generates log files.
Example: A large e-commerce website will have a collection that involves gathering data from web servers (tracking user requests and responses), database servers (monitoring queries and transactions), and possibly third-party services that the website interacts with.
Challenges and considerations: One of the key challenges in this step is to ensure that the various log formats and sources are compatible. Also, ensure that the collection process does not impact system performance.
2. Log Aggregation and Centralization
After the log collection, the next step is to merge different logs into a centralized system for effective management and analysis.
Example: An IT department in a multinational corporation will aggregate logs from different geographic locations, various departments (like HR, finance, operations), and multiple technology stacks into a single, accessible repository.
Challenges and Considerations: The main challenge here is dealing with the volume of data and the diversity of log formats. This stage requires ensuring data integrity during aggregation and setting up a scalable and accessible storage solution.
3. Log Processing and Normalization
Logs come in different formats depending on their source. Therefore, it requires processing and normalizing by converting them into a standard format for consistent analysis.
Example: An IT security team may get logs in different formats from various security appliances like firewalls, intrusion detection systems, and antivirus software. Normalizing these logs requires extracting the relevant data from each log type and converting it into a uniform structure like a common timestamp format and consistent categorization of event types.
Challenges and Considerations: Key challenges include creating normalization rules that accurately process diverse log formats. Also, this requires flexibility to adapt to new log types and maintain the fidelity of the original log data during this process.
4. Log Storage and Archiving
After collecting and normalizing the logs, the next step is to store them securely. This step ensures that log data is kept in a way that preserves its integrity and confidentiality.
Example: A financial institution must store transaction logs securely as they deal with sensitive data. It requires leveraging encrypted storage systems to safeguard data against unauthorized access yet remain accessible for audit logs and analysis.
Challenges and Considerations: The primary challenge here is to balance accessibility with security, especially for logs that contain sensitive information. Also, consider the sheer volume of data and efficient storage solutions that drive scalability and cost-effectiveness.
5. Log Analysis
This is a critical phase in log management since it requires analyzing the collected log data to extract meaningful insights. It involves looking for patterns, anomalies, and potential problems within the logs.
Example: A cloud computing environment will have log analysis that helps identify patterns, indicating inefficient use of resources. For instance, frequent spikes in CPU usage logs could signal the need for better resource allocation or optimization of processes.
Challenges and Considerations: The key hurdle here is data complexity since logs can be voluminous and contain a mix of mundane and critical information. So, effective log analysis often needs sophisticated tools and algorithms that sift through large datasets to find relevant insights.
6. Alerting
Continuously monitoring the log data helps detect IT issues in time. This step requires setting up systems that instantly flag unusual activities or potential problems as soon as they occur.
Example: Businesses emphasizing network security will have log monitoring that requires setting up alerts. These act as indicators of compromise, like multiple failed login attempts or unusual outbound traffic, which could signify a security breach.
Challenges and Considerations: The primary concern is defining what constitutes abnormal activity, which varies greatly depending on the context. It also requires finding a fine balance between sensitivity (catching every potential issue) and specificity (avoiding false alarms) to avoid alert fatigue.
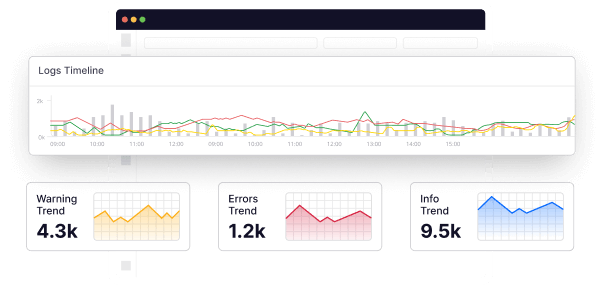
7. Reporting and Visualization
After analyzing the log, the final step involves communicating the insights from the log data. This includes creating reports and visual representations that are easily understood and acted upon.
Example: An online retailer must visualize website traffic logs to help identify peak shopping times and customer demographics. This may be presented as interactive dashboards showing user activity trends, page views, and conversion rates.
Challenges and Considerations: The key challenge here is to present the data meaningfully and actionable for different stakeholders. This requires managing log details and keeping its interpretation simple to ensure that the reports remain comprehensive.
Top Log Management Challenges in Cloud-First Era
Cloud computing has transformed the way organizations operate, bringing about unprecedented flexibility and scalability. However, the shift to a Cloud-First approach comes with its own set of challenges, particularly in log management.
Distributed Environments: Unraveling the Log Complexity
With applications spanning diverse cloud services, consolidating logs into a unified view becomes a logistical hazzard. The challenge lies in managing the distributed nature of logs efficiently.
- Each cloud service generates its own set of logs, often in different formats, making consolidation a logistical puzzle.
- Variability in log formats and structures among diverse cloud services hinders integration.
Implementing centralized logging solutions that can aggregate logs from disparate sources provides a holistic view. This simplifies the monitoring process and enhances troubleshooting capabilities.
Security Concerns
Security becomes paramount as organizations transition to the cloud, and safeguarding log data emerges as a critical concern. The challenge lies in ensuring the confidentiality and integrity of logs throughout their lifecycle, from transmission to storage.
- Log data moving between cloud services is susceptible to interception, posing a threat to sensitive information.
- Inadequate access controls can lead to unauthorized personnel gaining access to critical log files, compromising security.
You’d need to implement robust encryption protocols to secure log data during transmission, preventing unauthorized access during transit.
Scalability
As organizations expand their operations, the volume of generated logs experiences exponential growth, presenting challenges in effectively managing and processing this ever-increasing workload.
- Traditional log management solutions may encounter performance bottlenecks when handling large volumes of log data, impacting overall system efficiency.
- Scalability issues arise when the log management system lacks the capability to dynamically adjust to fluctuating workloads, leading to potential data processing delays.
By integrating scalable solutions and embracing cloud-native approaches, organizations can effectively address the challenges associated with the exponential growth of log volumes, ensuring optimal performance in managing and processing logs.
Integration Complexity
Integration with diverse cloud services poses a formidable challenge in the realm of log management. The unique log formats, APIs, and structures across various cloud platforms create a complex environment that demands careful consideration.
- Different cloud services generate logs in distinct formats, complicating efforts to create a standardized and integrated log management system.
- Variability in APIs among diverse cloud platforms introduces challenges in creating a cohesive and interoperable log management strategy.
Addressing integration complexity involves strategic tool selection and flexible solutions, enabling organizations to create a cohesive log management strategy that spans diverse cloud platforms.
Storage and Costs
As the volume of logs increases, storing them can be overwhelming for most enterprises given the costs associated with it. Making things worse are compliance requirements that demand certain logs to be stored for extended periods.
To navigate this situation, enterprises need to invest more in storage solutions that are scalable as well. And the cherry on top? Logs come in different formats and sadly, not all solutions support all formats.
To address this issue, you need to craft a sound log storage strategy that aligns with your business goals and budgets. There needs to be an emphasis on a cost-effective yet scalable solution that can be sustainable in the long run.
Log Management vs. Log Analytics vs. Log Monitoring
Let’s dive into the key differences, unraveling the unique roles each plays in shaping a comprehensive strategy for understanding and optimizing IT operations.
| Aspect | Log Management | Log Analytics | Log Monitoring |
| Definition | Involves the collection, storage, and organization of log data. | Involves the analysis of log data to extract meaningful insights, trends, and patterns. | Involves the real-time observation of log data to detect anomalies, patterns, or critical events, triggering immediate responses. |
| Key Purpose | Ensures a centralized repository of logs for troubleshooting, compliance, and auditing. | Extracts actionable intelligence from log data for proactive decision-making. | Provides real-time awareness for immediate issue detection and response. |
| Focus | Foundational – storage and retrieval of historical logs. | Analytical – extracting valuable information from logs. | Forward-looking – real-time alerts and responses. |
| Benefits | Simplifies troubleshooting, compliance, and auditing processes. | Aids in troubleshooting and performance optimization. | Enhances system reliability, minimizes downtime through immediate response. |
| Time Perspective | Historical – retrospective analysis of past events. | Present and Historical – focuses on both current and past data analysis. | Real-time – immediate observation and action. |
| Integration | Initial step for building an observability foundation. | Builds on log management, providing deeper insights. | Works alongside log management and analytics for comprehensive observability. |
Log management, log analytics, and log monitoring stand as distinct pillars, each with its own unique strengths. Whether you prioritize the foundational storage of historical data, the extraction of actionable insights, or real-time vigilance, the choice is yours.
Log Management Best Practices
Efficient log management is essential for maintaining a secure and optimized IT environment. Consider the following best practices to enhance your log management strategy:
Formulate a Strategy and Establish Policies
Formulating a log management strategy involves creating a structured plan for collecting, storing, and analyzing logs within an organization. Establishing clear policies around data handling, retention, and access is a fundamental best practice in the realm of IT operations.
A well-defined log management strategy serves as the foundation for a proactive and organized approach to handling logs while ensuring adherence to compliance standards and a structured framework for mitigating risks.
Identify What Needs to Be Logged and Monitored
Identifying what needs to be logged and monitored involves a meticulous process of determining the critical events, activities, and system components that warrant inclusion in the log management system.
The significance of this practice lies in its ability to focus log management efforts on the most pertinent information. By clearly defining what to log and monitor, organizations optimize resource utilization, streamline analysis, and ensure that logs align with security, compliance, and operational goals.
Understand How Your Logs Are Structured
Understanding how your logs are structured involves gaining insight into the formats and fields that compose log data. This is fundamental for harmonizing log entries, ensuring consistency, and facilitating effective analysis.
Consider this practice to be the groundwork for organized log management. By comprehending log structures, organizations streamline the parsing and interpretation of log data, enabling quicker troubleshooting and proactive identification of trends.
Adopt Centralized Logging
Adopting centralized logging involves consolidating logs from diverse sources into a singular repository. This best practice streamlines log management, fostering enhanced visibility, and simplifying the analysis of log data.
By aggregating logs in one central location, organizations gain a comprehensive overview of their IT ecosystem.
Use Indexing
The practice of using indexing involves creating structured indices for log data, significantly improving the speed and efficiency of log retrieval and analysis.
By creating searchable indexes based on relevant log fields, organizations expedite the process of retrieving specific information. This practice ensures that log analysis is thorough and enables quicker identification of critical events and trends within the log data. It contributes to overall operational efficiency and timely decision-making.
Implement Real-time Monitoring and Alerts
Implementing real-time monitoring and alerts involves continuously observing log data in real-time and configuring automated alerts to promptly respond to critical events.
This practice enables organizations to detect anomalies or potential threats as they happen, minimizing response times. Automated alerts ensure that IT teams are promptly notified of issues, allowing for timely investigation and resolution.
In a nutshell, effective log management boils down to clear strategies, precise identification, centralized logging, and real-time vigilance.
As we conclude, the next steps involve continual refinement, staying abreast of emerging technologies, and evolving strategies to ensure that log monitoring remains a dynamic and integral part of an organization’s digital resilience.
FAQs on Log Management:
What is a log management system?
A log management system is a tool that gathers, stores, and analyzes log data from various sources. It acts as a central hub for troubleshooting issues, monitoring system activities, and maintaining compliance.
How to do log management?
To manage logs effectively, create a plan, set policies, decide what to log, understand log structures, use centralized logging, implement indexing, and incorporate real-time monitoring practices.
What is the difference between log management and SIEM?
Log management handles log data organization, while Security Information and Event Management (SIEM) goes further by integrating logs with security information, offering advanced threat detection, and correlation capabilities.
Why is log management so important?
Log management is crucial for swift issue resolution, ensuring compliance with regulations, strengthening security measures, and gaining insights for proactive problem identification. It forms the backbone of a resilient and well-monitored IT environment.